Updated EC-Council CEH 312-50v8 PDF & VCE Free Download Now (11-20)
QUESTION 11
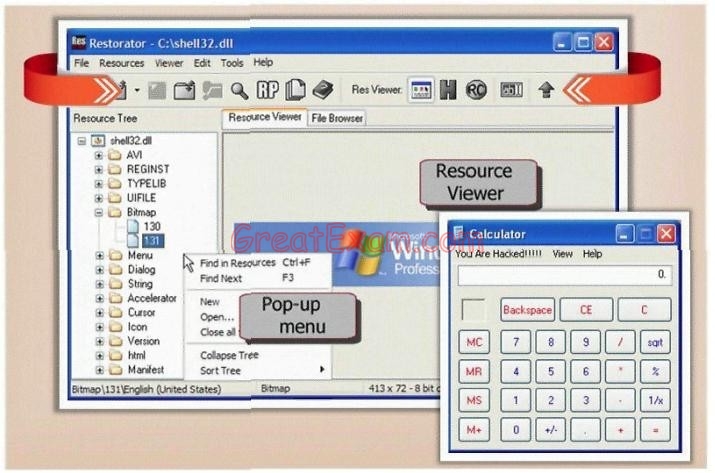
What type of Trojan is this?
A. RAT Trojan
B. E-Mail Trojan
C. Defacement Trojan
D. Destructing Trojan
E. Denial of Service Trojan
Answer: C
QUESTION 12
Maintaining a secure Web server requires constant effort, resources, and vigilance from an organization. Securely administering a Web server on a daily basis is an essential aspect of Web server security. Maintaining the security of a Web server will usually involve the following steps:
1. Configuring, protecting, and analyzing log files
2. Backing up critical information frequently
3. Maintaining a protected authoritative copy of the organization’s Web content
4. Establishing and following procedures for recovering from compromise
5. Testing and applying patches in a timely manner
6. Testing security periodically.
In which step would you engage a forensic investigator?
A. 1
B. 2
C. 3
D. 4
E. 5
F. 6
Answer: D
QUESTION 13
In Buffer Overflow exploit, which of the following registers gets overwritten with return address of the exploit code?
A. EEP
B. ESP
C. EAP
D. EIP
Answer: D
QUESTION 14
Web servers often contain directories that do not need to be indexed. You create a text file with search engine indexing restrictions and place it on the root directory of the Web Server.
User-agent: *
Disallow: /images/
Disallow: /banners/
Disallow: /Forms/
Disallow: /Dictionary/
Disallow: /_borders/
Disallow: /_fpclass/
Disallow: /_overlay/
Disallow: /_private/
Disallow: /_themes/
What is the name of this file?
A. robots.txt
B. search.txt
C. blocklist.txt
D. spf.txt
Answer: A
QUESTION 15
An attacker has successfully compromised a remote computer. Which of the following comes as one of the last steps that should be taken to ensure that the compromise cannot be traced back to the source of the problem?
A. Install patches
B. Setup a backdoor
C. Install a zombie for DDOS
D. Cover your tracks
Answer: D
QUESTION 16
Attackers target HINFO record types stored on a DNS server to enumerate information. These are information records and potential source for reconnaissance. A network administrator has the option of entering host information specifically the CPU type and operating system when creating a new DNS record. An attacker can extract this type of information easily from a DNS server. Which of the following commands extracts the HINFO record?

Answer: A
QUESTION 17
Bret is a web application administrator and has just read that there are a number of surprisingly common web application vulnerabilities that can be exploited by unsophisticated attackers with easily available tools on the Internet. He has also read that when an organization deploys a web application, they invite the world to send HTTP requests. Attacks buried in these requests sail past firewalls, filters, platform hardening, SSL, and IDS without notice because they are inside legal HTTP requests. Bret is determined to weed out vulnerabilities. What are some of the common vulnerabilities in web applications that he should be concerned about?
A. Non-validated parameters, broken access control, broken account and session management,
cross-site scripting and buffer overflows are just a few common vulnerabilities
B. Visible clear text passwords, anonymous user account set as default, missing latest security patch,
no firewall filters set and no SSL configured are just a few common vulnerabilities
C. No SSL configured, anonymous user account set as default, missing latest security patch,
no firewall filters set and an inattentive system administrator are just a few common vulnerabilities
D. No IDS configured, anonymous user account set as default, missing latest security patch,
no firewall filters set and visible clear text passwords are just a few common vulnerabilities
Answer: A
QUESTION 18
What is War Dialing?
A. War dialing involves the use of a program in conjunction with a modem to penetrate the modem/PBX-based
systems
B. War dialing is a vulnerability scanning technique that penetrates Firewalls
C. It is a social engineering technique that uses Phone calls to trick victims
D. Involves IDS Scanning Fragments to bypass Internet filters and stateful Firewalls
Answer: A
QUESTION 19
Steven the hacker realizes the network administrator of Acme Corporation is using syskey in Windows 2008 Server to protect his resources in the organization. Syskey independently encrypts the hashes so that physical access to the server, tapes, or ERDs is only first step to cracking the passwords. Steven must break through the encryption used by syskey before he can attempt to use brute force dictionary attacks on the hashes. Steven runs a program called “SysCracker” targeting the Windows 2008 Server machine in attempting to crack the hash used by Syskey. He needs to configure the encryption level before he can launch the attack. How many bits does Syskey use for encryption?
A. 40-bit encryption
B. 128-bit encryption
C. 256-bit encryption
D. 64-bit encryption
Answer: B
QUESTION 20
Bob waits near a secured door, holding a box. He waits until an employee walks up to the secured door and uses the special card in order to access the restricted area of the target company. Just as the employee opens the door, Bob walks up to the employee (still holding the box) and asks the employee to hold the door open so that he can enter. What is the best way to undermine the social engineering activity of tailgating?
A. Issue special cards to access secure doors at the company and provide a one-time only brief description
of use of the special card
B. Educate and enforce physical security policies of the company to all the employees on a regular basis
C. Setup a mock video camera next to the special card reader adjacent to the secure door
D. Post a sign that states, “no tailgating” next to the special card reader adjacent to the secure door
Answer: B
If you want to pass the EC-Council CEH 312-50v8 exam sucessfully, recommend to read latest EC-Council CEH 312-50v8 Exam Questions full version.






